IT Asset Disposition (ITAD): Your Comprehensive Guide to Secure and Sustainable IT Disposal for UK Businesses
What Exactly is ITAD and Why is it Essential for UK Businesses?
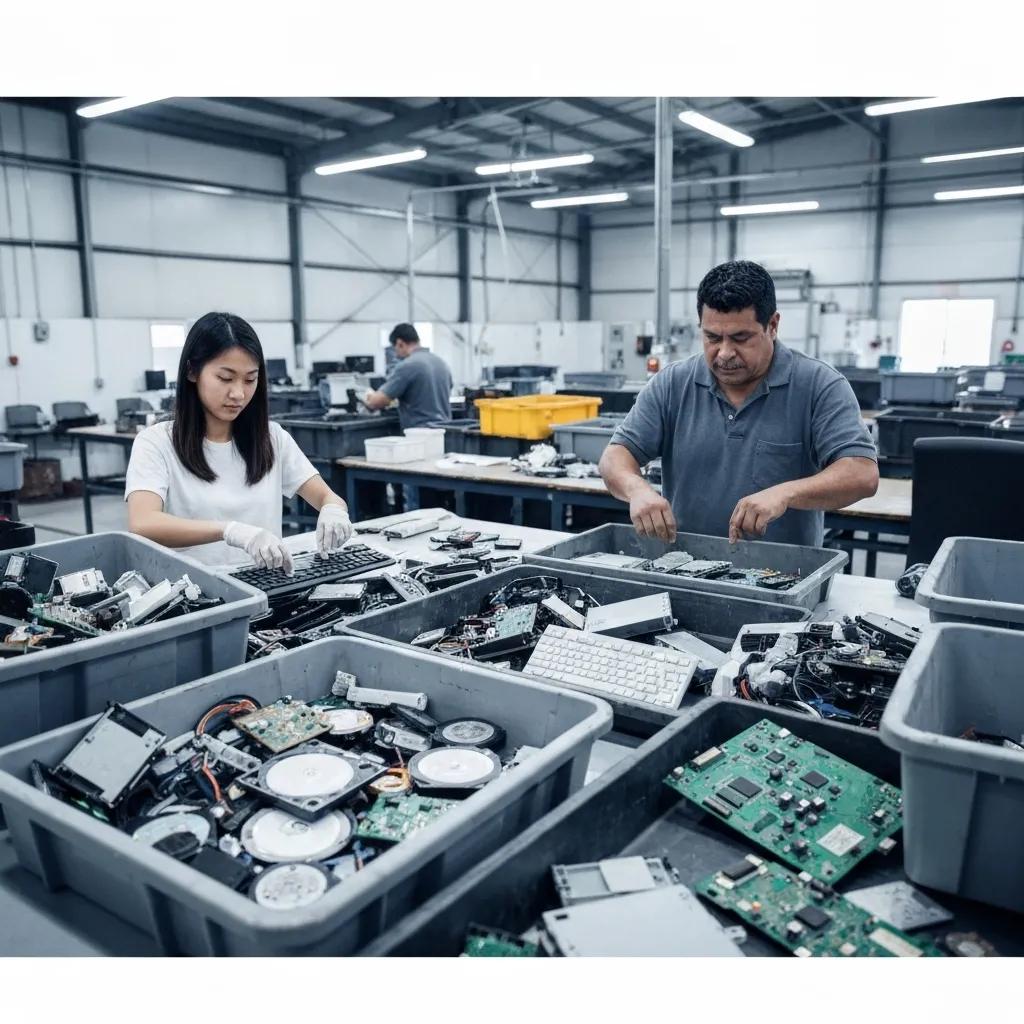
What Does the ITAD Process Entail?
Why is ITAD Absolutely Crucial for Data Security within UK Businesses?
How Does ITAD Actively Support Environmental Sustainability and the Circular Economy?
What Are the Key UK Regulations Governing IT Asset Disposal?
How Does GDPR Specifically Impact ITAD Practices in the UK?
| Requirement | Penalty Tier | Maximum Fine |
|---|---|---|
| Incomplete data erasure | Moderate (Record-keeping errors) | €10 million or 2% of turnover |
| Data breach from device disposal | Significant (Personal data leakage) | €20 million or 4% of turnover |
GDPR and Data Erasure Mandates - UK Focus
The General Data Protection Regulation (GDPR) requires that personal data on retired devices must be made permanently inaccessible prior to disposal. Failure to comply can lead to penalties of up to €20 million or 4% of global turnover. Utilising certified erasure tools, degaussing equipment, or physical destruction guarantees full compliance and helps prevent significant financial penalties.
What Are the WEEE Directive Requirements for IT Asset Recycling?
- Registering with an approved compliance scheme.
- Reporting the volumes of electronics placed on the market.
- Ensuring hazardous components are diverted from landfill.
WEEE Directive and IT Asset Recycling Obligations - UK
The Waste Electrical and Electronic Equipment (WEEE) Directive mandates that producers and businesses must collect, treat, and recover electronic waste under “producer responsibility” schemes. Essential duties involve registering with a compliance scheme, reporting the quantities of electronics supplied to the market, and ensuring hazardous components are not sent to landfill.
Which Other Standards and Certifications Guarantee ITAD Compliance?
How Does the ITAD Process Unfold, from Collection to Final Certification?
What Are the Essential Steps for Secure IT Asset Collection and Logistics?
What Data Destruction Methods Are Employed in ITAD?
| Method | Security Level | Typical Application |
|---|---|---|
| Software Erasure | High | Drives intended for reuse and refurbishment |
| Degaussing | High | Magnetic media requiring physical erasure |
| Physical Shredding | Maximum | Hard drives and SSDs that are beyond reuse |